Karsten Nohl height - How tall is Karsten Nohl?
Karsten Nohl was born on 11 August, 1981 in Germany. At 39 years old, Karsten Nohl height not available right now. We will update Karsten Nohl's height soon as possible.
-
6' 0"
-
5' 10"
-
5' 10"
-
5' 8"
Now We discover Karsten Nohl's Biography, Age, Physical Stats, Dating/Affairs, Family and career updates. Learn How rich is He in this year and how He spends money? Also learn how He earned most of net worth at the age of 41 years old?
| Popular As |
N/A |
| Occupation |
N/A |
| Karsten Nohl Age |
41 years old |
| Zodiac Sign |
Leo |
| Born |
11 August 1981 |
| Birthday |
11 August |
| Birthplace |
Germany |
| Nationality |
Germany |
We recommend you to check the complete list of Famous People born on 11 August.
He is a member of famous with the age 41 years old group.
Karsten Nohl Weight & Measurements
| Physical Status |
| Weight |
Not Available |
| Body Measurements |
Not Available |
| Eye Color |
Not Available |
| Hair Color |
Not Available |
Dating & Relationship status
He is currently single. He is not dating anyone. We don't have much information about He's past relationship and any previous engaged. According to our Database, He has no children.
| Family |
| Parents |
Not Available |
| Wife |
Not Available |
| Sibling |
Not Available |
| Children |
Not Available |
Karsten Nohl Net Worth
He net worth has been growing significantly in 2021-22. So, how much is Karsten Nohl worth at the age of 41 years old? Karsten Nohl’s income source is mostly from being a successful . He is from Germany. We have estimated
Karsten Nohl's net worth
, money, salary, income, and assets.
| Net Worth in 2022 |
$1 Million - $5 Million |
| Salary in 2022 |
Under Review |
| Net Worth in 2021 |
Pending |
| Salary in 2021 |
Under Review |
| House |
Not Available |
| Cars |
Not Available |
| Source of Income |
|
Karsten Nohl Social Network
Timeline
The data collected via “SnoopSnitch” can also be uploaded, with the user’s consent, to a database to support additional security analysis, which is shared on the "GSM Security Map" website.
In April 2018, Nohl presented on security in the mobile Android environment. Nohl and his colleagues analyzed Android firmware images from various smartphone vendors. In some cases, a so-called "patch gap" was found, where vendors had not applied all security patches that otherwise should have been present based on the monthly patch level date specified in the firmware. Nohl released an updated version of the open source “Snoopsnitch” app with new features to allow users to run tests on their Android phones to check for a "patch gap" on their device.
At the 31C3 in December 2014, Nohl presented the Android app "SnoopSnitch" as a possible countermeasure against various mobile network security attacks. On various smartphones models with Qualcomm chipset and root access, mobile network traffic can be collected and analyzed locally with "SnoopSnitch,” where the app gives the user information about the encryption and authentication algorithm being used by the network, the possibility for SMS and SS7 attacks, as well as the potential presence of IMSI-catchers.
At Black Hat 2014, Nohl and Jacob Lell presented on security risks associated with USB devices. The USB standard is versatile and includes many different classes of devices. Their research is based on the reprogramming of USB controller chips, which are widely used and found in USB sticks. There is no effective protection against reprogramming, so a harmless USB device can be converted and used as a malicious device in many ways.
At SIGINT-2013, Nohl gave a presentation on the insecurity of electronic car immobilizers used to prevent vehicle theft, documenting vulnerabilities in the three most widely used systems: DST40 (Texas Instruments), Hitag 2 (NXP Semiconductors) and Megamos (EM Micro).
At both Black Hat 2013 and OHM 2013, Nohl demonstrated that many SIM cards use the outdated and insecure DES encryption, undermining the privacy and security of mobile phone users. Through "Over The Air (OTA)" communication, such as SMS messages, it is possible to provide a SIM card with updates, applications, or new encryption keys. Such messages are digitally signed with DES, 3DES or AES. Nohl generated a Rainbow Table for 56-bit DES within a year based a on specially signed error message with known plain text. The resulting attack scenario: an attacker sends the victim a signed text message. With the help of the Rainbow Table it is then possible to crack the DES key of a SIM card in minutes and crack the internal key. (Known Plaintext Attack). This allows an attacker to send a signed SMS, which in turn loads a Java app onto the SIM card. These apps are capable of multiple actions, including sending SMS or sharing the location of the device. An attacker could, for example, command a device to send SMS messages to foreign premium services at the cost of the device owner. In principle, the Java Virtual Machine should make sure that every Java app can only access predefined interfaces. Nohl found that the Java sandbox implementations of at least two major SIM card manufacturers, including market leader Gemalto, are insecure and it is possible for a Java app to escape the sandbox environment and thus gain access to the entire SIM card. This makes it possible to duplicate SIM cards including the IMSI, authentication key (Ki) and payment information stored on the card.
At the 30C3 in December 2013, Nohl introduced the Android app "GSMmap". Initially designed for use on a Galaxy S2 or S3 (including root access), the app collects information on the level a mobile network secures its traffic. The collected data can be uploaded, with the app user’s consent, to a database that evaluates the security of mobile networks worldwide, based on selected protection capability criteria. The results of this analysis are displayed on the "GSM Security Map" website, where the security level of mobile providers are visualized on an interactive world map and made available for download as "country reports".
At Chaos Communication Camp 2011, Nohl and Luca Melette gave a presentation showing how GPRS networks do not securely encrypt their mobile traffic. The pair stated that they had recorded data transmissions in the networks of several German mobile providers, including Deutsche Telekom, O2 Germany, Vodafone and E-Plus. Several mobile service providers used either no or only insufficient encryption. With a modified mobile phone, mobile traffic could be read from within a radius of five kilometers.
In April 2010, Nohl, together with Erik Tews and Ralf-Philipp Weinmann, published details on the cryptographic analysis of DECT proprietary and secret encryption algorithm used (DECT standard cipher), which is based on reverse engineering of DECT hardware and descriptions from a patent specification.
At the 27C3 in December 2010, Nohl, together with Sylvain Munaut, demonstrated how mobile calls can be cut and decrypted with the help of converted cheap mobile phones and the open-source software OsmocomBB. The pair showed that the GSM encryption can be cracked "in about 20 seconds" and that calls can be recorded and played back.
Together with Henryk Plötz, Nohl gave a presentation in December 2009 documenting the flawed security of Legic Prime RFID security. The talk demonstrated how the system employed multiple layers of strange and obscure techniques in lieu of standard encryption and cryptographic protocols. This allowed cards to be read, emulated, and even for arbitrary master tokens to be created.
In the summer of 2009 Nohl introduced the A5 / 1 Security Project. The project demonstrated an attack on the GSM encryption standard A5/1 using Rainbow Tables. With the help of volunteers, the key tables were calculated in a few months and published on the 26C3 in December 2009.
Nohl was part of the project group deDECTed.org [11], which in 2008 at 25C3 pointed out serious deficiencies in the DECT protocol.
As early as 2008, the hacker group THC had begun with the pre-calculation of key tables for A5 / 1, but probably never published the tables because of legal problems.
Together with Henryk Plötz and CCC Berlin's, Starbug, Nohl gave a presentation in December 2007 on how the encryption algorithm used in Mifare Classic RFID smart cards was cracked. The Mifare Classic Card has been used in many micropayment applications, such as the Oyster card, CharlieCard, or the OV Chipkaart for payment.
Nohl grew up in the Rhineland area of Germany and studied electrical engineering at the Heidelberg University of applied sciences from 2001 to 2004. From 2005 to 2008, he earned his PhD at the University of Virginia on Implementable Privacy for RFID Systems. Since 2010 Nohl has served as the Managing Director and Chief Scientist of the Berlin-based consultancy and think tank, Security Research Labs. Karsten has also served as interim CISO for the Indian corporation Jio from 2014 to 2017, as well as, for the Indonesian corporation Axiata in 2017.
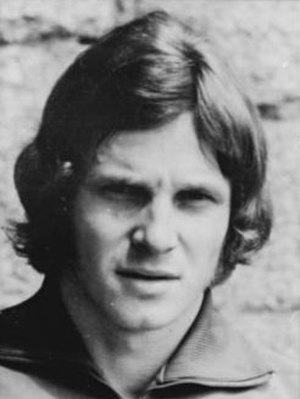
Karsten Nohl (born August 11, 1981) is a German cryptography expert and hacker. His areas of research include GSM security, RFID security, and privacy protection.